The introduction of the General Data Protection Regulation (GDPR) marked a significant shift in the global data privacy landscape as the first major comprehensive data privacy and security regulation. At Sequoia, we saw this not as a challenge but as an opportunity to reinforce our unwavering commitment to data privacy and security.
Our Pledge to Data Privacy
Our clients trust us with sensitive information, including that of their employees, and that is not something that we take lightly. Our privacy practices are built to ensure the security of the data that we receive in compliance with GDPR. But we don’t stop at compliance. Our philosophy is to go above and beyond, embedding privacy into the DNA of our projects and products from the get-go.
The Backbone of Our Commitment: Technical and Organizational Measures
We’ve instituted robust technical and organizational measures (TOMs) that stand as the bulwark against data threats. From cutting-edge threat modeling to comprehensive disaster recovery plans, our measures aren’t just built to only comply with the requirements of GDPR but are meant to provide industry leading data privacy and security, reflecting our deep understanding of the sensitivity of the data we steward.
- Threat Modeling: We begin by conducting threat modeling exercises, meticulously identifying potential vulnerabilities and risks to our data infrastructure. This proactive approach allows us to stay ahead of emerging threats and implement appropriate safeguards.
- Comprehensive Disaster Recovery Plans: Our comprehensive disaster recovery plans are designed to ensure business continuity and data integrity in the face of events both expected and unexpected. From natural disasters to cyberattacks, we are prepared to swiftly recover and minimize any potential impact on our operations.
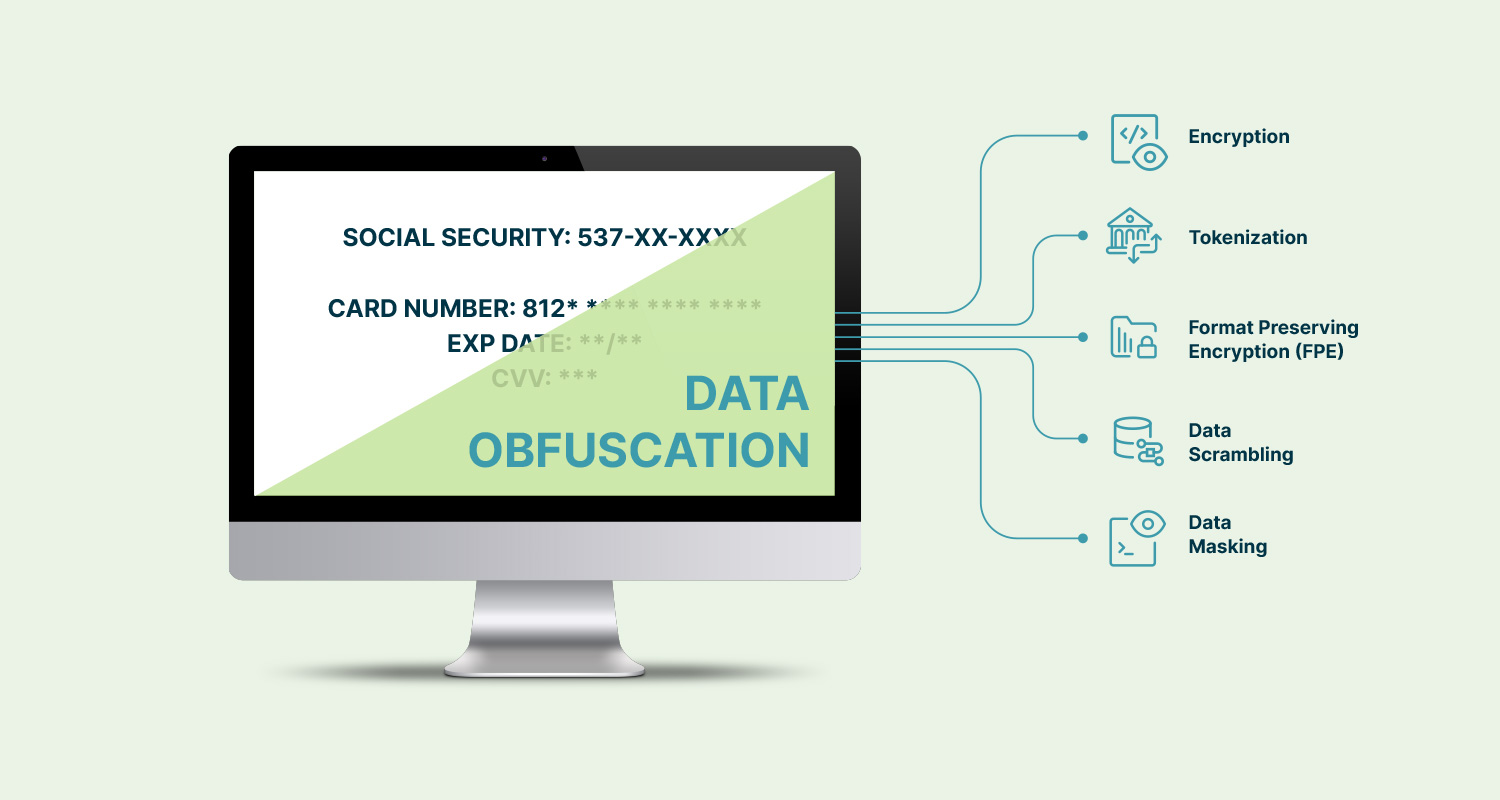
- Data Encryption: Sensitive data is encrypted both in transit and at rest using industry-leading encryption algorithms. This ensures that even if intercepted, the data remains unintelligible and unreadable to unauthorized parties, providing an additional layer of protection against data breaches.
- Access Control Mechanisms: We enforce strict access control mechanisms to limit access to sensitive data only to authorized personnel. Role-based access controls and multi-factor authentication protocols are implemented to minimize the risk of unauthorized access and insider threats.
- Regular Security Audits: Our systems undergo regular security audits and assessments to proactively identify and address any vulnerabilities, such as penetration testing, ISO, and SOC2 Type 2.
- Employee Training and Awareness: Employees are required to undergo training on data security best practices both upon joining Sequoia and annually, fostering a culture of security awareness throughout the organization. Awareness campaigns ensure that all employees understand their role in maintaining data security.
- Incident Response Protocols: In the event of a potential security incident, we have thorough incident response protocols in place to investigate and respond. From initial detection to resolution, these protocols ensure a swift and effective response, minimizing any potential impact on our data and operations.
- Continuous Monitoring: Our systems are continuously monitored for suspicious activities and anomalous behavior. Real-time monitoring enables us to detect and respond to potential security threats promptly, mitigating risks and ensuring the ongoing protection of our data assets.
Partnering with Integrity: Vendor and Partner Reviews
Before we engage with any vendor or partner, we conduct thorough reviews of their data security and privacy practices, ensuring they comply with our high standards. This due diligence extends to regular assessments, ensuring sustained compliance and security in our partnerships.
- Thorough Vendor and Partner Reviews: Conduct comprehensive evaluations of data security and privacy practices before engaging with any vendor or partner to ensure that their practices with our stringent standards.
- Ongoing Assessments: Perform regular assessments to verify continued compliance with our data privacy and security agreements and GDPR.
A Framework of Trust: Data Agreements
Our relationships are built on trust and reinforced by rigorous data privacy agreements.
- Data Processing Agreements: Our agreements include GDPR data processing agreements, as applicable, delineating the responsibilities and obligations related to the processing of personal data as mandated by GDPR.
- Formalized Trust: Beyond mere formalities, our data processing agreements solidify the trust between us and our clients and, reinforcing our commitment to safeguarding personal information and respecting individuals’ privacy rights.
Empowering Data Subjects
Central to GDPR is the empowerment of individuals over their data. Our comprehensive Standard Operating Procedures (SOP) for Data Access, Correction, and Deletion Requests ensure every individual’s rights are respected and acted upon promptly, reflecting our commitment to not just compliance but to the ethical treatment of data.
- Comprehensive Standard Operating Procedures (SOP): Implementing detailed procedures for handling Data Access, Correction, and Deletion Requests in accordance with GDPR.
- Respect for Individual Rights: Ensuring that every individual’s rights regarding their data are acknowledged, respected, and promptly acted upon.
- Prompt Response: Acting promptly upon Data Access, Correction, and Deletion Requests to ensure completion of the requests not just in compliance with GDPR timelines but in a timely fashion.
GDPR: Our Blueprint for Data Management
Our GDPR compliance framework is the blueprint upon which we build our data management practices. It ensures that every aspect of our operations, from vendor engagement to data processing and purging, is in strict adherence to GDPR principles, safeguarding the right to privacy and data protection.
- Comprehensive GDPR Compliance Framework: Establishing a robust framework that guides all aspects of our data management practices in strict adherence to GDPR principles.
- Safeguarding Privacy Rights: Ensuring that our operations, including vendor engagement, data processing, and purging, prioritize the protection of privacy rights and data security.
- Holistic Approach: Integrating GDPR compliance into every facet of our operations to foster a culture of privacy and data protection throughout the organization.
- Continuous Adherence: Commit to ongoing compliance with GDPR through regular assessments and updates to our policies and procedures.
- Transparency and Accountability: Maintaining transparency and accountability in our data management practices building trust with our clients and stakeholders.
At Sequoia, GDPR compliance isn’t just a legal obligation—it’s our promise to our clients. Through strict policies, rigorous protocols, and a steadfast commitment to privacy, we stand as guardians of data, ensuring its protection and upholding the rights of individuals. Join us in our journey towards a future where privacy is not just a right, but a way of life.