Cyber-attacks are on the rise! This phrase, or similar ones, have been appearing in the news and in information security articles for many years, and will continue to do so. We all know data is valuable to organizations, and it directly translates to services and money. But data is also valuable to the “bad guys.” A 2021 Forbes article explained the value of personal information on the dark web and offered the following observations:
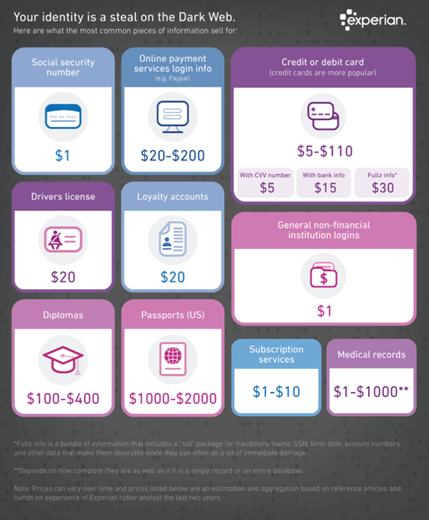
- A full set of data was valued at $1,010.
- Online banking logins cost an average of just $40, with full credit card details including associated data costing between $14 and $30.
- US credit cards are valued at significantly less – $17 on average – than those of other nations, thanks to the high supply.
- Prices for hacked social media accounts seem to be dropping across the board. A hacked Gmail account has halved in value over the last year, dropping from $156 to just $80.
- Dark web markets are overflowing with listings of hacked cryptocurrency trading accounts and wallets such as Coinbase, LocalBitcoins, Kraken, Cex and more. A US verified LocalBitcoins account costs $350, rising to $610 for Coinbase and $810 for a Kraken account.
This interesting infographic from Experian provides further insight.
Attacker Motivation
Although attackers may have different motivations (state-sponsored espionage, corporate intellectual property theft, ideology, hacktivists, personal enjoyment, etc.), most are looking to make easy money. To do this, attackers are getting more sophisticated in their attacks and more creative as well, using all sorts of social engineering techniques to get what they want.
Attack Methods
It is often easier for an attacker to send out a few thousand phishing emails or SMS-phishing (smishing) text messages and wait for someone to fall for it, rather than figuring out how to identify if a vulnerability exists on a particular system, exploit it and then hope to get to the loot – the personal data, the PII and PHI.
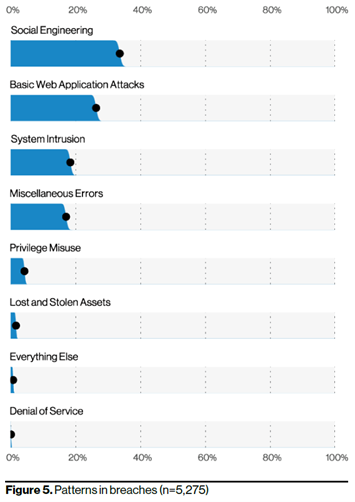
According to the 2021 Verizon DBIR, social engineering attacks that resulted in reported data breaches accounted for the largest percentage of attacks than any other category (graph below).
Business Email Compromise (BEC) attacks have been gaining ground in the last few years and have become the most devastating type of social engineering attack for companies worldwide. Ransomware attacks have also been on the rise. Both types of attacks leverage social engineering tactics to infiltrate systems and gain access to data and in the case of ransomware, holding data hostage (usually by encrypting it) for ransom.
Smishing attacks where the attacker pretends to be the CEO or CFO of the company asking an employee to urgently purchase gift cards for a particular purpose and provide the card number and the numbers or a photo of the back of the card, is another very common attack causing headaches and financial pain to many individuals and organizations. According to the FTC, “In the first nine months of 2021, over twice as much money was reported lost on Target gift cards than any other brand. Google Play gift cards were next, followed by Apple, eBay, and Walmart cards.”
Sometimes, attackers also call victims directly from a fake phone number to carry out the scam. It is trivial for an attacker (or anyone with access to the internet) to research a company on social media such as LinkedIn, identify a company’s employees and C-level executives and then do research on the internet to find their phone numbers and other personal information about them. All this data is abundantly available online and on the dark web. A scammer can do the research and build the company and employee profiles within a matter of hours and then carry out the attacks.
What You Can Do
The FTC has issued guidance about gift card scams over the years. Here are some good tips:
- Keep your receipt and contact the retailer that issued the gift card. The FTC maintains a list of popular retailers and how to reach them about gift card fraud.
- File a police report. The FTC notes doing this may help you get assistance from the gift card issuer.
- Report the fraud to the FTC. Include as much information as you can, including times, dates, phone numbers or email addresses, and screenshots of messages. The FTC can’t resolve individual cases, but it investigates activity and shares fraud reports with relevant local law enforcement.
- Report the fraud to your state attorney general. Much like reporting fraud to the FTC, your state’s attorney general investigates larger fraud issues rather than resolving individual cases.
What Organizations Can Do
User awareness training is key here – people are the last line of defense! All the technologies in the world cannot save you if a user takes the wrong action.
- Talk about it often! The FTC states simply: “Gift cards are for gifts, not for payments.”
- New hires are often unaware that they can be targeted and may have no knowledge of such scams. Raising awareness about these scams at your company meetings or even smaller departmental meetings and corporate communications works well and reminds employees about this risk and what they should do, or more importantly, what not to do.
- Perform your own social engineering tests towards your own company employees to assess their awareness and train them.
- To reduce the risk of systems and data compromise from phishing emails, put in place a good email security filtering solution and do regular phishing campaigns and tests for your workforce.




