In this blog, we will discuss Sequoia’s current approach to encrypting data in our AWS S3 infrastructure. We understand the importance of protecting sensitive data and have implemented client-side encryption in addition to the disk encryption provided by AWS. This combination is designed to provide an extra layer of security for our clients by encrypting the data needed by our services where such data is stored.
Encryption Implementation
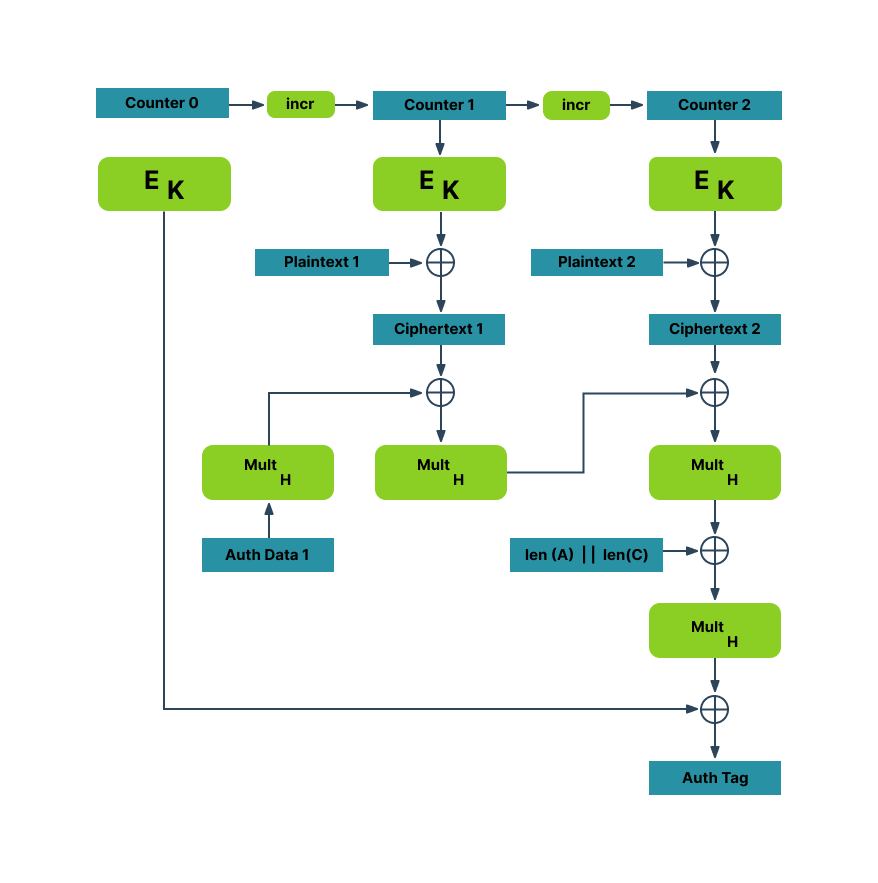
At Sequoia, we utilize Galois Counter Mode (GCM) with Advanced Encryption Standard (AES-256) symmetric encryption to protect client data. GCM is a popular mode of operation for block ciphers, combining the confidentiality of symmetric encryption with the authenticity of a message authentication code (MAC). GCM works by using the Counter (CTR) mode of encryption with a MAC based on Galois field arithmetic. The CTR mode generates a keystream that XORs with the plaintext to create ciphertext. The same keystream is used to create a MAC for the ciphertext and associated data.
GCM’s efficiency is one of its key benefits, as it allows for parallel processing of multiple blocks and does not require pre-computation or additional storage. Additionally, GCM provides strong security guarantees, including resistance to known plaintext and chosen plaintext attacks. By utilizing GCM and AES-256 encryption, we are confident in our ability to protect sensitive data and maintain the confidentiality of our clients’ information.
Here is a NIST diagram:
Key Management
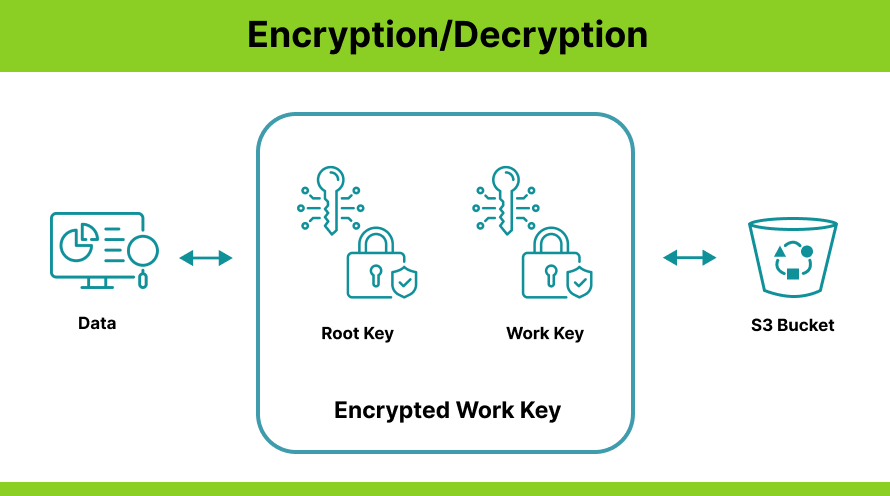
Sequoia key management combines a work and a root key. This combination generates an encrypted work key used to encrypt Sequoia data. This approach masks the actual key used for cryptographic operations such as encryption and decryption and makes it difficult for attackers to compromise both keys and gain access to the encrypted data.
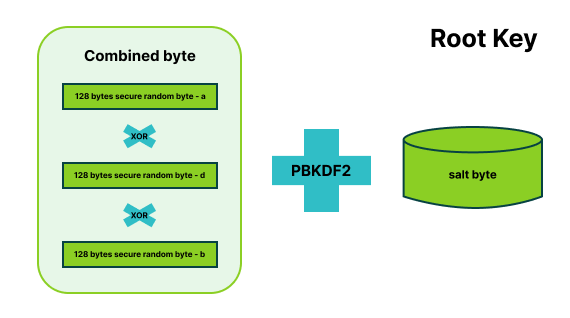
A root key is a module-specific intermediate key, which gets generated during the runtime of the application. It is generated by combining multiple random bytes. The root key is generated by an XOR operation of three different 128-byte random bytes (a, d, and b bytes), which yields a combined byte. A salt byte generated by specific randomly-generated strings with 48 bytes limits the risk of using precomputed hashes for attacks. Finally, a HMAC PBKDF2 function is applied to the combined key with salt key and repeats the process for n number of iterations to produce a root key.
A work key is a cryptographic key that is used to protect sensitive data by encrypting it using a symmetric encryption algorithm. The key is generated by a module-specific work key which is a 48 byte character string randomly generated with highly secure methods using a /dev/random file or os.random() function. It is typically used in conjunction with a block cipher mode of operation (Sequoia, for instance, uses GCM) which provides additional security features like integrity protection and authentication.
The encryption of data is completed by the following steps:
Step 1: Generate a plain work key
Step 2: Create an encrypted work key with plain work key root
Step 3: During runtime, both the modules should decrypt these encrypted work keys using their root keys and apply this key for encryption and decryption operation
Plain keys are never available anywhere and these are always encrypted using the respective module root and salt.
References
- Dworkin, Morris. “Recommendation for Block Cipher Modes of Operation: Galois/Counter Mode (GCM) and GMAC.” CSRC, 28 Nov. 2007, https://csrc.nist.gov/publications/detail/sp/800-38d/final.




