Sequoia Trust Center
Coming through for clients
At Sequoia, mutual trust is the foundation on which we build all our relationships. For over 23 years, Sequoia has provided the guidance clients need to care for their people and their business. When it comes to matters of data, technology, and security, our approach is based on investing in enterprise-class security features, an experienced and committed team, and continuous improvement.
Components
We extend trust through our service infrastructure and platform, with particular focus on security, compliance, and availability.
Security
We take security seriously and will continue to invest heavily in this area
More

Assessment
We undergo annual third-party assessment of our control framework
More

Status
See the current availability and performance status of Sequoia systems
Check status

Best Practices
See our recommendations and reminders for secure system access
View
If you are a security researcher and have an issue to report to us, please submit it to our bug bounty program
Report a Security Issue
Security
Sequoia has invested heavily in security infrastructure and staffing over its 21-year history. Components of our security program are outlined below:
Governance
Sequoia has appointed a Chief Information Security Officer (CISO) to lead the Security & IT function and develop policies and procedures to monitor and manage risks. Our cybersecurity program is supported by operations, product, engineering, and legal.
Security Policy
Sequoia’s Acceptable Use Policy (AUP) applies to Sequoia team members regarding the use and/or access of company information systems and data. The AUP includes guidance on information security and practices and emphasizes the scope of individual responsibilities in adhering to company policies, applicable laws, and regulations.
Cyber Security Risk Management
Sequoia undergoes internal and external third-party risk assessments to identify areas where we can improve our security controls and processes and strengthen our security posture.
Application Security
Data Encryption
Sequoia uses strong encryption algorithms such as AES-256 for data at rest and TLS 1.2/1.3 for HTTPS connections so that data is encrypted both in transit and at rest (when stored).
Patch & Vulnerability Management
Endpoint Security & Monitoring
Sequoia’s endpoints are secured using advanced solutions to detect and respond quickly to malicious attacks. We also leverage web filtering solutions to prevent malicious internet traffic. Systems are monitored 24/7 by a variety of technologies and our SIEM is monitored 24/7/365 by a leading MSSP.
Security Awareness
Sequoia team members are trained frequently on security best practices, how to avoid phishing attacks, and how to properly handle and protect sensitive data.
Privacy
Sequoia’s Privacy policy can be found here.
Road Map
Our security team continues to drive forward with additional investments, including implementing additional machine learning and AI capabilities to existing detection tools, staffing an internal incident response and detection team, amplifying our existing third-party testing program to increase testing frequency, and implementing a bug bounty program. As part of our ongoing strategy of continuous enhancement, please continue to check this Trust Center to learn about additional security assets that we will make available to clients.
Assessments
Sequoia undergoes annual SOC 2 Type II + HITRUST, ISO 27001, ISO 27017, and ISO 27018 assessments, which demonstrates our continued focus on establishing and complying with our control framework around protecting systems and data. The assessment reports and other documentation is available for review by visiting Sequoia’s Security Documents Hub at https://trust.sequoia.com/
Latest Blog Posts

Active Cyber Defense Using Red Teams

Zero Trust in Action: Layered Access Controls for SaaS Applications

DOL Confirms Cybersecurity Guidance Applies to All ERISA Plans
How Sequoia Empowers Team Members to Defend Against Cyber Attacks

Strengthening Sequoia’s Data Security with SaaS Solutions: A Comprehensive Approach

Navigating the Cybersecurity Landscape: Sequoia’s Comprehensive Approach

Elevating Data Privacy: Sequoia’s Journey Towards GDPR Excellence
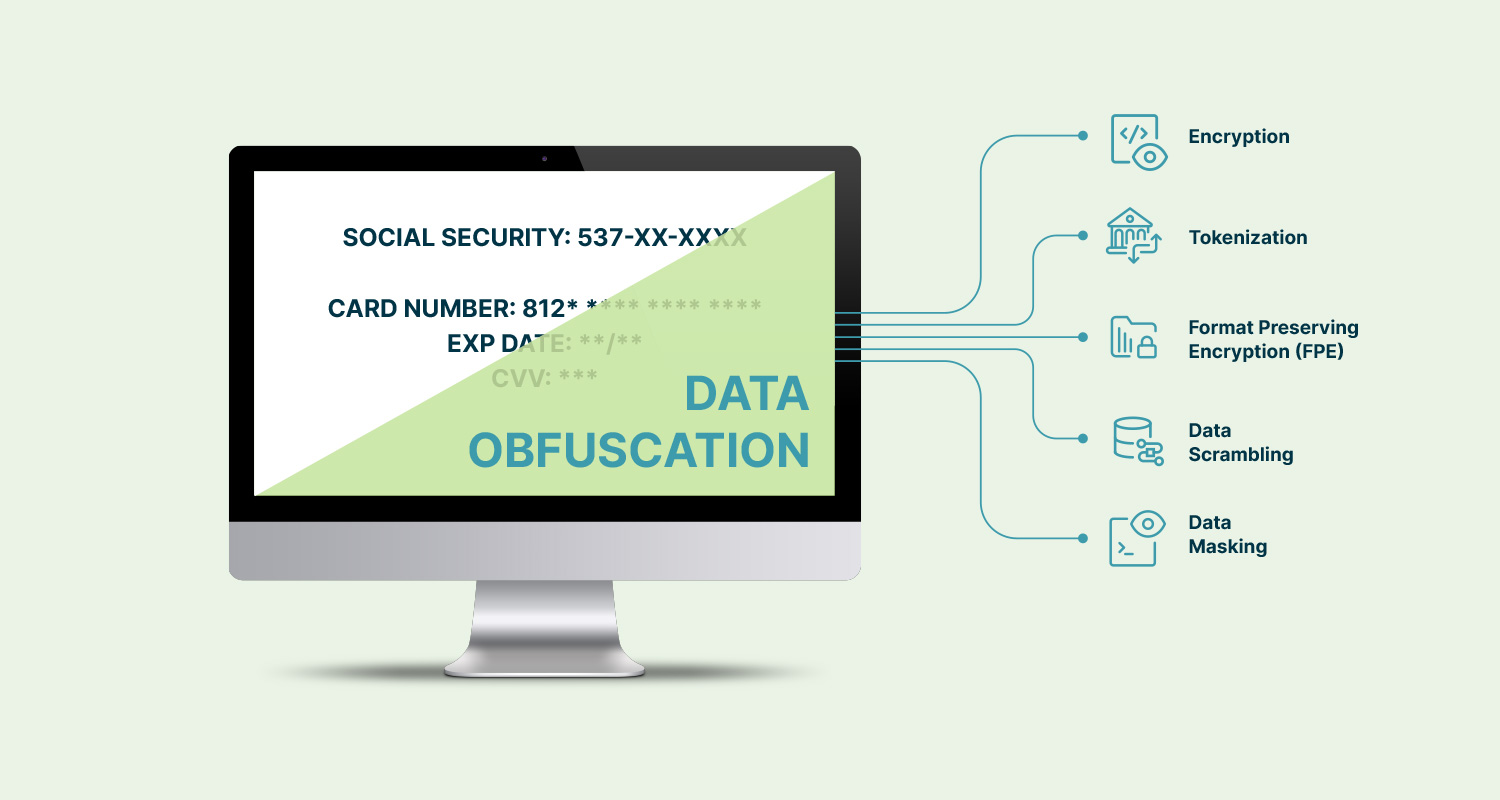
The Role of Data Obfuscation in Sequoia’s Data Protection Strategy

Securing Sequoia’s Digital Communication: A Deep Dive into DMARC Implementation

Unlocking Cybersecurity Excellence with the OODA Loop

Revolutionizing HR Management: Integrating Generative AI into Sequoia’s Platform

Essential Cybersecurity Practices: Safeguarding Your Digital World

Adding Certifications to Safeguard Your Data

A Comprehensive Guide to Client Data Segregation for Enhanced Data Protection

Sequoia’s Approach to S3 Encryption

Announcing Sequoia’s Bug Bounty Program

The Value of Information and Why Attackers Send Text Messages to Your Phone

Hiscox Cyber Readiness Report

Policies for Remote Work: Cybersecurity
Cyber Liability in the Time of Covid: Ransomware

Cyber Liability Insurance – 10 Tips to Consider

2020 Cyber Risk Landscape – Let’s Do A Deep Dive

Guide to Cyber Protection
Best Practice Recommendations
Sequoia clients can use these helpful reminders to ensure secure access when using the Sequoia People Platform.
Recommendations for Employers:
- Enable SSO (Single Sign On)
- Enable Multi-factor authentication (MFA)
- Enforce strong passwords and rotate passwords on a frequent basis
- Follow the Sequoia Trust Center for any new security alerts
- Share the CISA Avoiding Social Engineering and Phishing Attacks
- Ensure your employees know that Sequoia system emails are sent to their work email leveraging your corporate domain, not to their personal emails. Exceptions:
- Dependents will be sent system emails to whichever email they signed up with
- Early-stage companies who sign-up without an established domain (rare)
Upcoming Enhancements to the Sequoia People Platform:
- MFA will be applied to non-SSO access to our mobile app for extra security
- As an extra reassurance to your people that they are in the right place, your company logo will now be shown as an interstitial step during the login process (right after email verification)
Recommendations for Employees:
- Sequoia notification emails will always come from an @sequoia.com email address
- Access to the Sequoia portal is always through a @sequoia.com domain, example: login.sequoia.com, admin.sequoia.com or px.sequoia.com
- As one of our employees, your Sequoia notifications will come to your work email, never to your personal email.
- Note the exception: Your dependents will receive notifications to whatever email they signed up with
Phishing attempts are unfortunately all too common. Here are some general tips on staying vigilant:
- Always check who the email was sent from. Don’t simply act on familiar aesthetics.
- Check for grammatical errors, incorrect spelling, and unusual capitalization
- Avoid acting impulsively to urgent messages – this is a common scammer tactic
- Double check the URL links in any email by mousing over them. Look for the proper domains. When in doubt, type in the URL address manually.
- If you receive an email that looks suspicious or you are not the intended recipient, don’t click on any links and report it to your IT and Security team at your organization


